TECH GUIDES FOR PRACTICAL BUILDERS
Learn faster. Build cleaner. Evolve with confidence.
UpBrightSkills publishes hands-on tutorials, architecture notes, automation playbooks, and security-focused engineering guides for people who like to ship real work.
Fresh articles surfaced for quick learning
Focused technology tracks to explore
Published guides across the knowledge base
Trending reads picked by reader activity
Featured Posts
Editor-picked posts with practical steps, cleaner layouts, and useful technical takeaways.

Can AI Replace Humans? Let's Have an Honest Conversation
Read Guide
IT Hygiene – Why the Basics Still Matter Today
Read Guide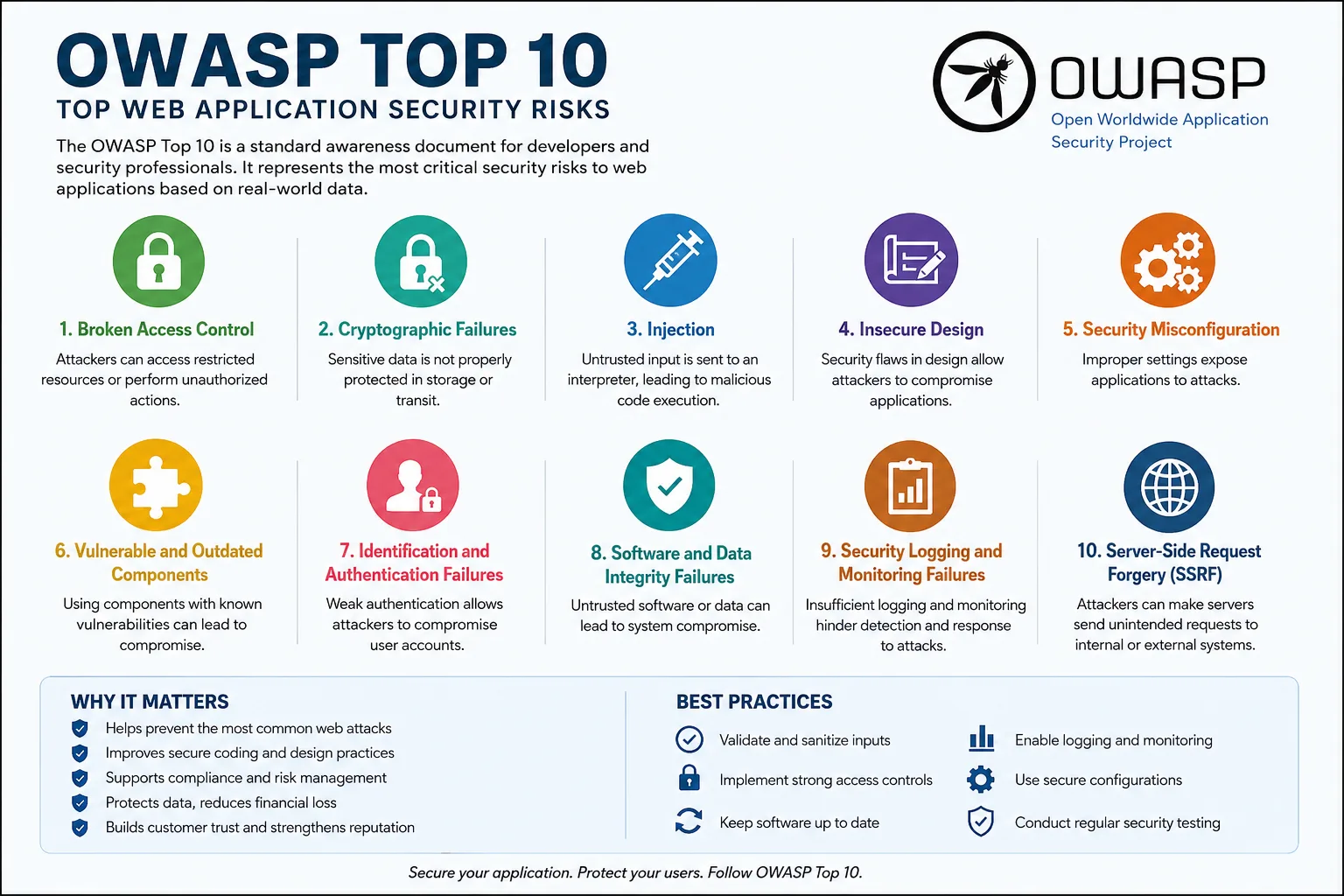
OWASP Top 10: Why It Matters for Every Business and Developer
Read Guide
ISO/IEC 42001 Explained: The AI Management Standard You Need
Read Guide
Beyond the IDE: How Google Antigravity 2.0 is Redefining Agentic Software Development
Read Guide
A Guide to Safeguarding Against Cyber Frauds
Read Guide
AI in DevOps: Your New Teammate Who Never Sleeps
Read Guide
AI Ethics
Read Guide
AI - Token Efficiency & Smarter Prompting
Read GuideExplore by Topic
Jump straight into the areas that matter to your next build.
Latest Articles
Recent notes, walkthroughs, and implementation patterns from the UpBrightSkills library.
WHY READ UPBRIGHTSKILLS
Built for people who need usable answers, not theory overload.
Each article is shaped around real implementation work: commands that fit together, screenshots and examples where useful, and enough context to help you make the right trade-off.
Start LearningSecurity-aware by default
Guides include operational and security context so your builds stay maintainable.
Hands-on technical depth
Step-by-step workflows for Linux, DevOps, cloud, automation, and platform setup.
Fast paths to action
Clear CTAs, topic filters, and related reads help users keep momentum.
